Last Updated: October 30, 2025
Ways people leave data online?
There are many ways people leave information online. They can do this consciously or unconsciously. People mostly leave the information on social networks and various platforms as well as on websites. It is advisable to leave as little data as possible, so as not to get into unpleasant situations. Everything left on the internet is hard to permanently delete. Be careful how you act, be careful. The Internet has changed (and continues to change) the way we live and work for the better, that’s for sure. This change, unfortunately, comes at an extremely high cost – our privacy. Privacy on the Internet means the level of privacy and security of personal data published in the virtual world. Internet privacy is a very broad term that encompasses various factors, techniques, and technologies used to protect sensitive and private data, as well as communication channels.
When meeting new people on the Internet, take special care. Don’t give away your data, be careful, you never know who is on the other side. Do not give photos, place of residence, phone number. Every activity on the internet leaves a digital mark. Whether we are creating content on social networks, installing an application, visiting a website, playing an online game, or using an Internet browser. What remains for us is information – personal, which we share ourselves, but also those that we unconsciously leave, such as our “behavior” on a website. Never compromise someone’s privacy by screenshotting and sharing private messages with other people or a group of people, knowing that the person whose messages are in question would not want that.
Password Manager – Security Application
A password manager application that will be useful to you. More and more users are using this app. Safety and security should come first. A password manager incorporates a lot of benefits. A password manager is an application that will generate, store, download, and manage passwords and other user credentials. He could also be your relief when it involves maintaining your privacy, interface, and connectivity with other devices similarly as dual authentication are a number of the advantages that are important when managing passwords.
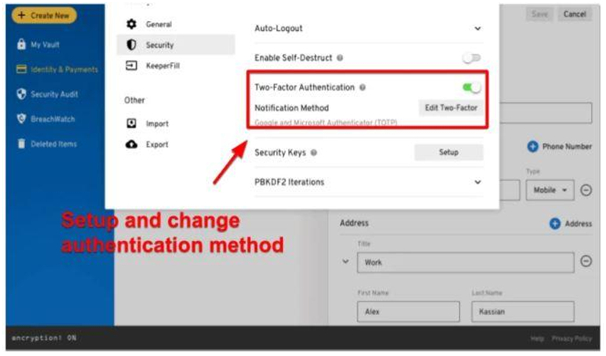
Two-factor authentication: Using multiple factors to authenticate your main application. This will be within the variety of a master password, plus a secret stream or PIN provided by another device. Another factor can be through biometrics. Password managers allow you to gather and save all of your passwords and login information for various accounts in one easy-to-access application that will log you into any service you have got subscribed to with just some clicks. It’s important to use different passwords for each site/service you utilize, use complex passwords – a mixture of uppercase and lowercase letters, characters, and numbers.
How to Protect Online Privacy?
When visiting websites, make sure that only they, and not third parties, collect the necessary information via cookies. You can do this by setting your internet browser to automatically reject third-party cookies. This significantly reduces the possibility of data theft and various malversations, which most often occur through some fake ads that are displayed on the website you initially visited. Never use a username from one account as a password on another.
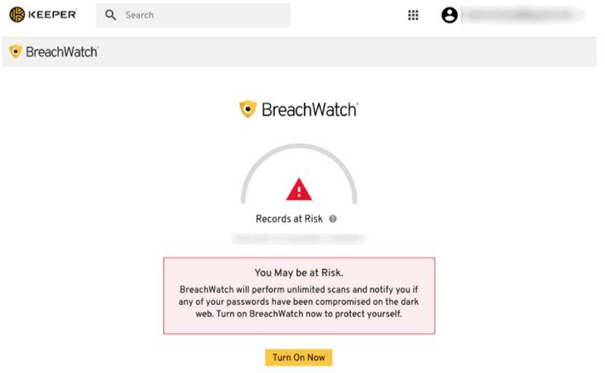
Set privacy on social media so you have more or less control over the content you post. If you’re not sure something is worth posting, learn to stop. Additionally, be sure to sign out of all accounts after you end the session, whether it’s social media or various pages where you have a profile. Never leave accounts active, as this makes them an even easier target for various attacks. Smart use of the Internet implies the implementation of all available protection measures, both on the part of servers and Internet service providers, and on the part of us, users, when leaving confidential information and personal data, especially if we are connected via a public unsecured wireless network or public computer.
Regular Updates as a Step Towards Security
You need regular software updates on all devices to stay safe and secure. Hackers are non-stop active and only seek carelessness or negligence to take advantage of your mistakes. If you do not take your data into account, the documents may be compromised. Don’t put yourself in that situation. As developers fix one security hole, hackers find another very quickly. It’s a game that has no end. That’s why we have updated so often. Don’t put your computer system at risk by avoiding regular updates. You may one day regret it bitterly. A large number of device owners do not pay attention to the fact that a new system has come out, so there is an unpleasant situation that the device will not work properly if it bugs. The software must be updated regularly for the device to work quickly and stably.
Use public computers only to search for information and not to connect to any of the existing Internet accounts (e-mail, social networks, banking services, etc.). Public computers are available to everyone, so all the data on them is available to everyone: from search history to the information needed to log in to Internet accounts.
Be careful what you open on the Internet
Before you click on an internet browser, no matter who sent it to you, think twice! Various computer viruses are programmed so that it only takes one click to download them to the device you are using to infect it. Computer viruses can be programs that allow unhindered access to all the data you have on your device, even if a third party enters your Internet accounts and changes your password. Also watch out for messages in which anyone asks you to send them a bank pin, password, or some other sensitive personal information.
Always be focused, stay confident. Use a password manager that makes it a lot easier for you. All kinds of people are on the Internet, don’t be gullible, beware.

